J1 (cipher): Difference between revisions
No edit summary |
No edit summary |
||
| Line 12: | Line 12: | ||
| structure = {{wpl|Unbalanced Feistel network}} | | structure = {{wpl|Unbalanced Feistel network}} | ||
| rounds = 127 | | rounds = 127 | ||
| cryptanalysis = | | cryptanalysis = Correlation attack using 2<sup>45</sup> ciphertexts against several weak long-term keys. As of 2018, no feasible attack has been found against long-term keys used operationally. | ||
}} | }} | ||
| Line 33: | Line 33: | ||
==Cryptanalysis== | ==Cryptanalysis== | ||
Despite its age, J1 remains a substantially strong algorithm, especially when compared to some of its contemporaries such as {{wpl|DES}}. This is largely thanks both to the large number of rounds used and the extremely low number of bits generated during encryption, as well as the use of a long-term key. The long key length of 242 bits also helps to increases security. Analysis of some of the publicly available long-term keys indicate that the bits were specifically chosen with the goal of defending against basic differential and linear cryptanalysis, nearly 20 years before the techniques were publicly discovered, but around the same time that major intelligence agencies around the world became aware of it. | Despite its age, J1 remains a substantially strong algorithm, especially when compared to some of its contemporaries such as {{wpl|DES}}. This is largely thanks both to the large number of rounds used and the extremely low number of bits generated during encryption, as well as the use of a long-term key. The long key length of 242 bits also helps to increases security. Analysis of some of the publicly available long-term keys indicate that the bits were specifically chosen with the goal of defending against basic {{wpl|differential cryptanalysis|differential}} and {{wpl|linear cryptanalysis}}, nearly 20 years before the techniques were publicly discovered, but around the same time that major intelligence agencies around the world became aware of it. | ||
However, the security of the J1 cipher is heavily dependent on the long-term key | However, the security of the J1 cipher is heavily dependent on the long-term key; overall weak long-term keys can open up the cipher to a variety of attacks. Furthermore, the simple, periodic key schedule allows for some strong correlation attacks against the cipher despite the presence of a randomly generated IV. | ||
Currently, the best attack against J1 is | Currently, the best attack against J1 is a {{wpl|correlation attack}} published in January 2018, which uses 2<sup>45</sup> ciphertexts to break a number of weak long-term keys. Long-term keys that were known to have been used operationally were found to be strongly resistant to this attack. Due to this difference, J1 is not yet considered broken. | ||
==Technology/Hardware== | ==Technology/Hardware== | ||
Revision as of 03:32, 23 May 2018
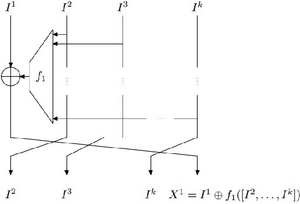 A generic contracting unbalanced Feistel network, similar to J1. | |
| General | |
|---|---|
| Designers | Unit 28, Air Force Intelligence Directorate |
| First published | 1974 (standardized) 1998 (declassified) |
| Cipher detail | |
| Key sizes | 242 bits |
| Block sizes | 36 bits |
| Structure | Unbalanced Feistel network |
| Rounds | 127 |
| Best public cryptanalysis | |
| Correlation attack using 245 ciphertexts against several weak long-term keys. As of 2018, no feasible attack has been found against long-term keys used operationally. | |
The J1 cipher, also known by its code name of Nisan (Arabic: نيسان, English: April), is a symmetric key block cipher with a key length of 242 bits and a block size of 36 bits. It was developed by Unit 28 (Cryptography) of the Riysian Air Force Intelligence Directorate (Mukhabarat) as a cipher for the encryption of military, government, and diplomatic teletype and later data networks. The algorithm was issued in 1974, but due to its sensitive nature, it was only declassified in 1998, after the hardware using it had largely been retired. It is notable for being the first fully electronic Riysian cipher, and for using a structure similar to an unbalanced Feistel network, which was considered highly complex in its time.
Though it has been superseded by more modern algorithms, the J1 continues to make a substantial impact on Riysian cryptography. Lessons learned from its development and cryptanalysis continue to be utilized in the development of cipher algorithms, as well as some of its underlying concepts. In particular, the concept of the unbalanced Feistel cipher remains very popular, with even the recent J3 algorithm using a modified Feistel network.
History
Description
J1 uses a block size of 36 bits, with a key size of 242 bits and an initialization vector (IV) of 61 bits randomly generated from an LSFR. The internal structure is similar to an unbalanced Feistel network, with four branches and 127 rounds. Its key schedule is very simple, forming two subkeys each 121 bits in length by splitting the main key in half, with a periodic repetition every 121 rounds. Like most ciphers of its age, it is implemented in specific hardware.
An unusual feature of the J1 cipher is that it accepts two keys, a short-term key and a plug-in long-term key. The short-term key is the nominal secret key for encryption, while the long-term key is a printed circuit board with unique wiring per series. This long-term key performs a function similar to both the S-boxes and P-box of modern block ciphers, accepting 9 individual inputs - each similar to an S-box - of 4 bits each, and then performing a permutation as in a P-box. The implementation of the long-term key is similar to the concept of a tweak. The long term key has an effective size of anywhere from 83 to 94 bits, depending on the key's wiring.
Though designed as a block cipher, J1 was almost always used in a stream cipher mode. When used as a stream cipher, the block cipher is run through its full 127 cycles, with a function on the long-term key circuit board extracting a single bit. To encrypt a single 5-bit Baudot character, 13 bits are required, for a total of 1,651 cycles; 3 bits of these 13 are randomly chosen to be dropped, with the remaining 10 bits used to doubly-encrypt the character in a 5+5 scheme. As the IV is needed in the decryption process, the 61-bit IV would be transmitted in the clear as part of a 125-bit/25-character "synchronization sequence".
Cryptanalysis
Despite its age, J1 remains a substantially strong algorithm, especially when compared to some of its contemporaries such as DES. This is largely thanks both to the large number of rounds used and the extremely low number of bits generated during encryption, as well as the use of a long-term key. The long key length of 242 bits also helps to increases security. Analysis of some of the publicly available long-term keys indicate that the bits were specifically chosen with the goal of defending against basic differential and linear cryptanalysis, nearly 20 years before the techniques were publicly discovered, but around the same time that major intelligence agencies around the world became aware of it.
However, the security of the J1 cipher is heavily dependent on the long-term key; overall weak long-term keys can open up the cipher to a variety of attacks. Furthermore, the simple, periodic key schedule allows for some strong correlation attacks against the cipher despite the presence of a randomly generated IV.
Currently, the best attack against J1 is a correlation attack published in January 2018, which uses 245 ciphertexts to break a number of weak long-term keys. Long-term keys that were known to have been used operationally were found to be strongly resistant to this attack. Due to this difference, J1 is not yet considered broken.